We already have a popular post for the configuration of IFD setup with CRM 2013 and CRM 2011. Now we are updating this post to support CRM 2015.
Microsoft have a compatibility listing for CRM 2015 here: http://support.microsoft.com/kb/3018360
The Development Setup
Once again we are running this configuration as a test environment for development. As such we will be running, we are running the server on a Hyper V server. A single VM machine, that is running a fully patched version of:
- Windows 2012 R2 SP2 64 Bit – (MSDN File: en_windows_server_2012_r2_x64_dvd_2707946)
- SQL 2014 R2 64 Bit – SQL Server 2014 Standard Edition x64 – (MSDN File: en_sql_server_2014_standard_edition_x64_dvd_3932034) – Patched to SP2
- Microsoft Dynamics CRM Server 2015 (x86 and x64) – DVD (English) – (MSDN File: en_microsoft_dynamics_crm_server_2015_x86_x64_dvd_5853339)
NOTE: The Domain we have used for setup with this dev server is: iwebscrm15.com You can substitute your domain in place throughout these step by step IFD instructions CRM 2015.
Installing CRM 2015
We pretty much followed a combination of these instructions:
http://blogs.msdn.com/b/niran_belliappa/archive/2013/11/05/step-by-step-installing-dynamics-crm-2013-on-windows-server-2012.aspx
During the install, we were asked to install services associated with the services required for CRM 2015.

We Selected all options on install:

We selected the default account for authority. Note that the blog referenced above suggests a dedicated account for security. As we are setting up a dev environment we did not bother with this.

IMPORTANT
Create a new Website with port 5555

As we intend to set up the Email Router service on this server later, we set this server “VSERVER06” in this instance as the server for email router service:
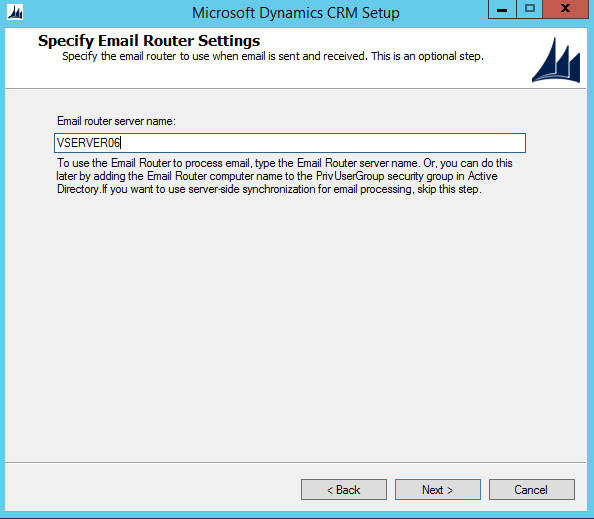
We set “CRM2015” As the default initial test environment deployment.

Reporting Server defaulted to the server name/reportserver

We received a few warnings about the install:
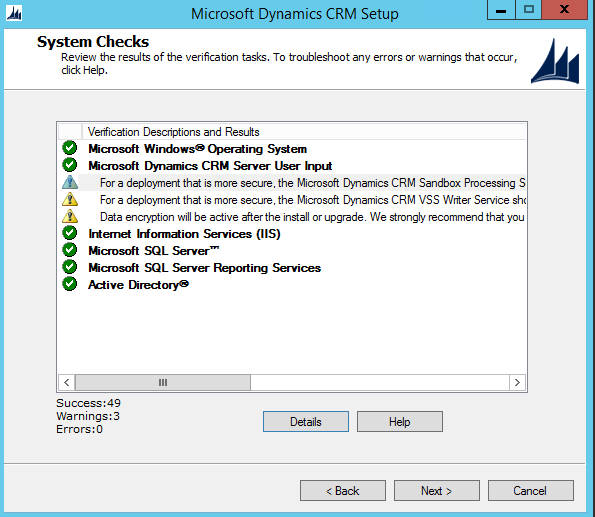
For a deployment that is more secure, the Microsoft Dynamics CRM Sandbox Processing Service should be run under a least-privileged domain user account that is not shared by other Microsoft Dynamics CRM services on this computer.
For a deployment that is more secure, the Microsoft Dynamics CRM VSS Writer Service should be run under a least-privileged domain user account that is not shared by other Microsoft Dynamics CRM services on this computer.
Data encryption will be active after the install or upgrade. We strongly recommend that you copy the organization encryption key and store it in a safe place. For more information, see http://go.microsoft.com/fwlink/?LinkId=316366.
The only one of real interest in our Dev environment would be the last item. making a backup of data encryption keys is always a good idea.
Test First
Test that your CRM setup is working. Go to the local computer name (ours is vserver06) on the correct port: http://vserver06:5555
We called our Deployment of CRM – “CRM2015″ So the URL redirects to: http://vserver06:5555/CRM2015/main.aspx
Because we were were logged in as the server administrator, we were able to load

Apply a Wildcard SSL Certificate
In CRM, the accessing of deployments is handled by the sub domains. So if we call a deployment “business1″ we will access that as: https://business1.domain.com
For testing, we purchased a standard Wildcard SSL certificate that applied that to the IIS Server
In our case we registered a test domain: iwebscrm15.com and set the SSL wildcard to: *.iwebscrm15.com and applied that cert to the server.
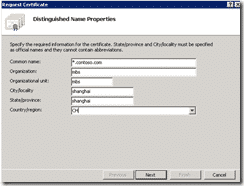
Application for a certificate
Here, I will be a wildcard certificate, for example, describes how to create a certificate:
1) Open IIS Manager
2) Click the server name in the main screen double click Server Certificates
3) In the right panel, click Create Certificate Request…
4) fill in the following diagram each column, click Next
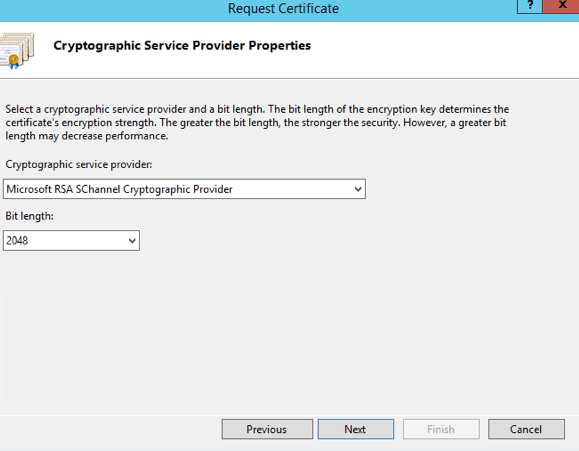
5) Cryptographic Service Provider Properties page change the Bit Length to 2048 click Next.
6) In the File Name page, enter C: \ req.txt , and then click Finish. (You can save it any place you like, with any name)
7) Open the certificate in Notepad, and copy the contents.

This is the text that is pasted into the Start SSL Certificate request page to generate the certificate:
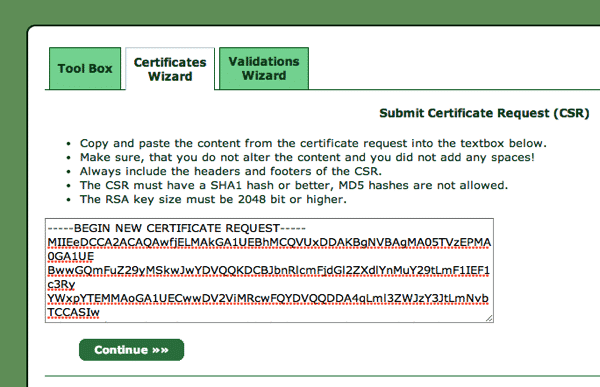
8) After you finish generating the certificate text in StartSSL.com you get a bunch of code that looks similar to the request code. Copy that generated code
9) Paste the code back into a new Text / Notepad Document on the Web server, but call it something that ends in .cer (not .txt).
10) back to the IIS Manager, click No. 3) Step graph Complete Certificate Request …
11) Select the the file you created at point 9 above to complete the request.
12) Click OK.
Note: We did get an error message: Access is denied. (Exception from HRESULT: 0x80070005 (E_ACCESSDENIED))
In this instance, it turned out to be a crappy Microsoft Error. After doing some research, we found that it was likely meaningless and the cert installed correctly. We rebooted the machine and logged in again, to find that the CERT was there installed as we wanted it to be.
Binding site for the default SSL certificate
1) Open IIS Manager.
2) In the Connections panel, expand Sites , click Default Web Site.
3) In the Actions pane, click Bindings.
4) In the Site Bindings dialog box, click Add.
5) Type select HTTPS.
6) SSL Certificate , select the certificate you just created *. contoso.com , and then click OK.

Ours is *.iwebscrm15.com
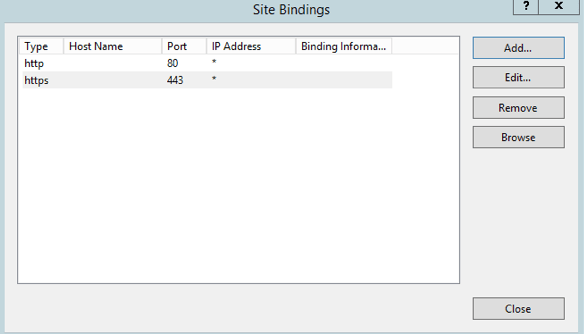
7) Click Close.
For the CRM 2015 binding site SSL certificate
This is in effect repeating the above process like you did for the default certificate, but using a different port (444 for example). This way you are binding the same certificate to the two websites in your IIS instance.
1)Open IIS Manager.
2) In the Connections panel, expand Sites , click CRM Web Site.
3) In the Actions pane, click Bindings.
4) In the Site Bindings dialog box, click Add.
5) Type select HTTPS.
6) SSL Certificate , select the certificate you just created *. contoso.com .
7) Port to select a different 443 (e.g. 444 ) and port number, and then click OK


8) Click Close.
DNS configuration
We are going to add a few DNS “A” records so that the records listed in point 1-4 below in DNS Goal are resolving correctly to the IP address of your CRM server.
There are two ways you can achieve the desired result. But first lets understand the desired result.
- We make the assumption that your server is running at least one static IP address.
- Because this is Internet Facing, that IP needs to be accessible to the world.
- That same IP can be used for access to your server both internally on the matching we are playing with, and externally form anyone on the net.
Lets Get Basic
Start a Command Prompt, and work out what your IP address of the server is.
Click START > RUN > CMD
Type IPCONFIG – Enter
Under the name: IPv4 Address is a number that looks like: 66.34.204.220
That is Your IP Address of the Server.
The DNS Goal
Make sure that when you PING xxx.domain.com that it points to that IP address. Both for the world and for you when you do that on your server.
(xxx is the sub domain that we are about to configure.)
To configure CRM, we need some sub domains to point to the server IP.
Adding records in DNS like this:

- sts1.domain.com
- auth.domain.com
- dev.domain.com
- Your ORG name. org.domain.com (Where ORG is the CRM deployment name of your organization or organizations), e.g.
- crm2015.iwebscrm15.com (We usually set up a dev environment with CRM2015 being the year of the version. Just something we select to do).
- adfs.domain.com (used for reference to the ADFS server)
- one for the root domain so that domain.com points to the same server. (This is for the ADFS logout URL)

We have two setup here: CRM and CRM2015. So we need to configure crm.iwebscrm15.com and crm2015.iwebscrm15.com (Not necessary but our choice for this instance).
Test DNS
You must be able to ping all of those names and get the correct server IP address. Both from computers on the internet, and from the server. At the command prompt, type “ping sts1.iwebscrm15.com” for example with our config. Ping them all to be sure you get them correct.
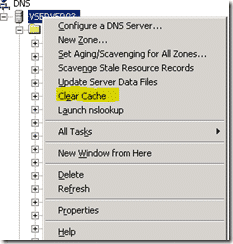
Note: If you have added the DNS records, but still encounter name resolution problems, you can try running on the client ipconfig / flushdns to clean up the cache. You can also click the DNS server root and click CLEAR CACHE so that the server is responding with the latest updates.
Note: Don’t bother proceeding past this step if you cannot ping your sub domains internally and externally correctly.
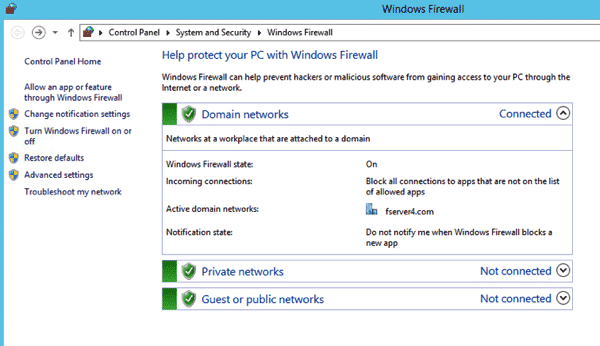
Firewall configuration
You need to set the firewall to allow the CRM 2015 and the AD FS 3.0 port used by the incoming data stream. HTTPS (SSL) is the default port 443.
For Initial setup testing etc. We recommend just turning the thing off. Better start from a place where it does not muck you around, then turn it all back on after you are successful.
1) In Windows 2012 I can’t frigging work out how to find anything. Literally! But most things you can search for. As is the case here if you search for “Firewall”. Select the firewall option:

2) Select Turn Windows Firewall on or off
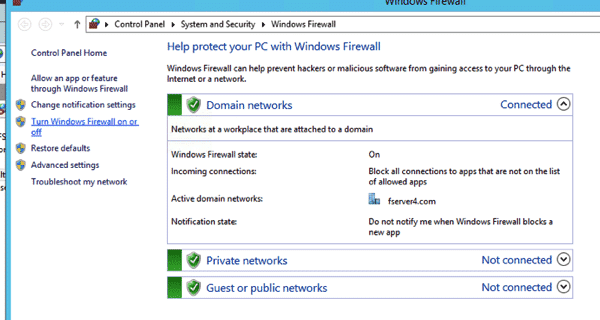
4) Turn Off or On Firewall

Just turn it all off for now. (Remember to come back, turn it on and allow access for the unusual port 444 that you configured earlier for the SSL on the CRM site. But for testing and setting up… the last things you want is to be banging your head agains a firewall.

Configuration Claim-based authentication –internal access
Configure the internal access Claim-based authentication requires the following steps:
- Install and configure AD FS 3.0
- Set Claims-based authentication configuration CRM 2015 server.
- Set the Claims-based authentication configuration AD FS 3.0 server.
- Test claims-based authentication within the access.
Install and configure ADFS 3.0
CRM 2015 with a variety of STS provider ( STS Provider ) together. This article uses Active Directory Federation Services (AD FS) 3.0 to provide a security token service (security token service ).
Note: AD FS 2.0 will be installed to the default site, so install AD FS 3.0 , you must have CRM 2015 installation in the new site. (Remember we said that earlier)
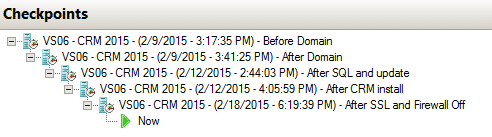
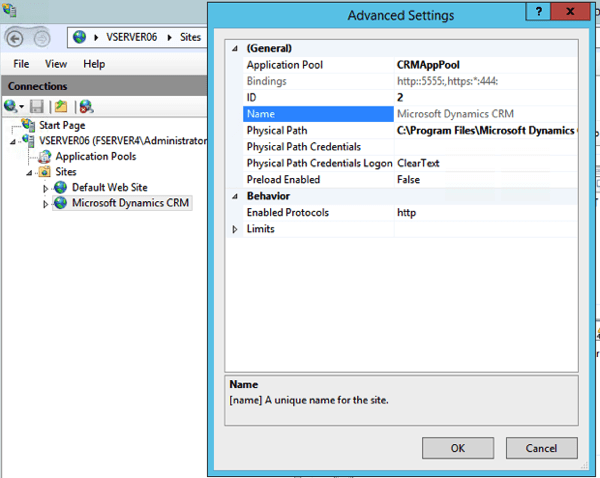
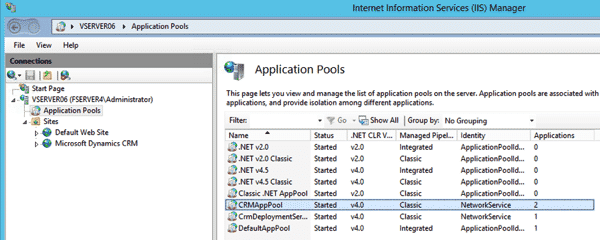
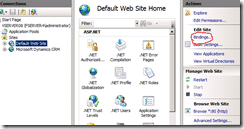
IIS Looks like this if it is correctly installed: 
If you only see the default website with CRM installed in that. Start AGAIN!
If you have it all correct at this point. Probably a good time to take a SnapShot (backup of the virtually system) and label it something you remember.
Install ADFS Server Role
From Server Manager – Add A Server role for: Active Directory Federation Services
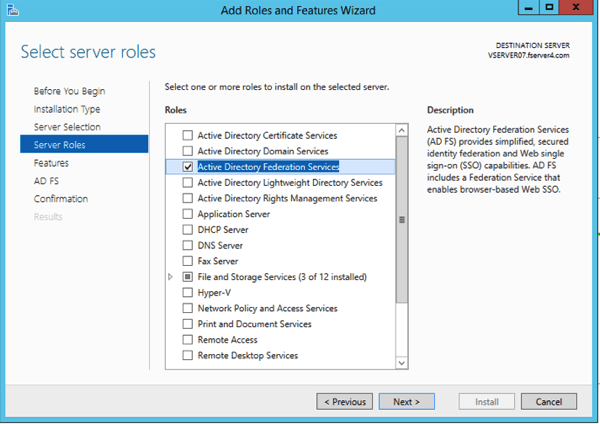



Click Install at the last step.
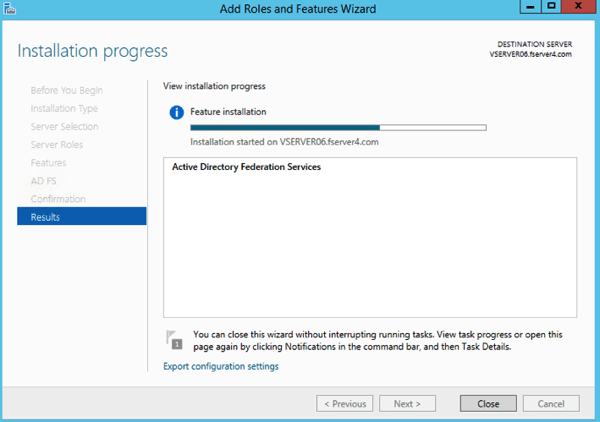
After if Finishes:
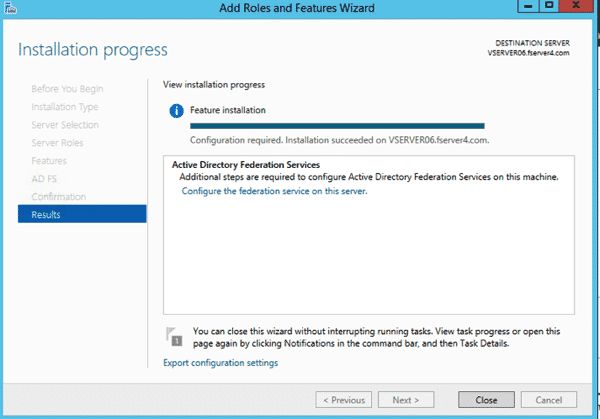
Click the Configure the Federation Services on this server.
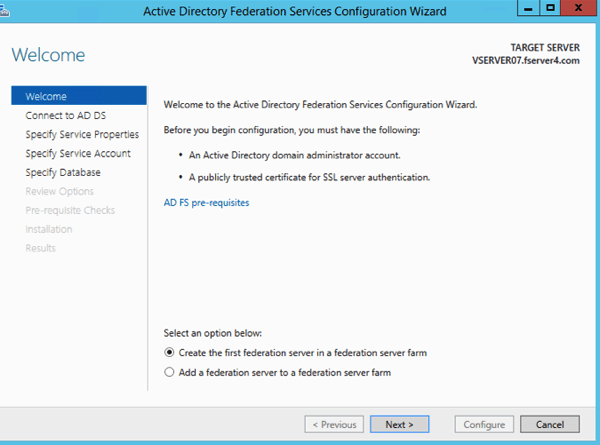
Configure AD FS 3.0
1 Click on Configure the federation service on this server.
2 In the AD FS 3.0 Management page , click AD FS 3.0 Federation Server Configuration Wizard .
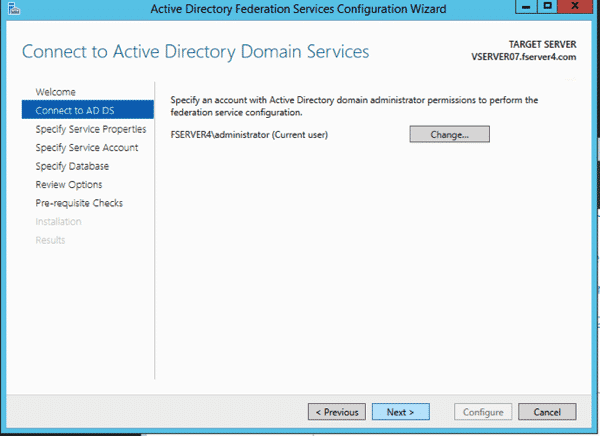
3 In the Welcome page , select Create the first federation server in a federation server farm, and then click Next.
4 Select next to continue with the current administrator (must be a domain admin).
5 Choose your SSL certificate (the one we created and imported above i.e. *.iwebscrm15.com ) ,add a Federation Service name ( Selecting the second one for the dropdown in this instance iwebscrm15.com, don’t select the one with the wildcard in the name, so not the *.iwebscrm15.com for example.), then Select a Service Display Name for your business – selecting the one that is NOT starting with a *, then click Next.

6 Open PowerShell and run the following command: “Add-KdsRootKey -EffectiveTime (Get-Date).AddHours(-10)”
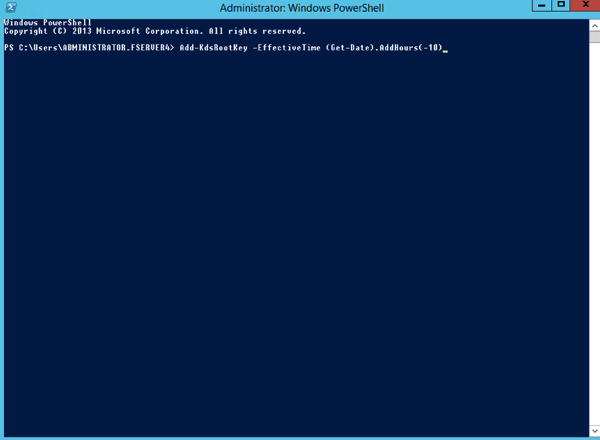
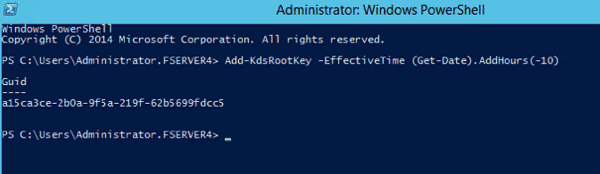
If you don’t you will se the error: Group Managed Service Accounts are not available because the KDS Root Key has not been set.
7 We specified the Administrator account for the service account, as security is not our primary concern here with a Dev environment. You could and probably should use a defined account for a production environment.

7 Create a database on this server using Windows Internal Database (we suggest using the SQL instance in the step below), click Next.

Or use the local SQL instance etc if you have one. (Because we have SQL installed on this same server. We are using this SQL instance for the database host.

8 Review Options click Next


10 You should see a message that “This Server was successfully configured

11 Close out the Instillation progress window


Verify the AD FS 3.0 is working
Follow the steps below to verify that the AD FS 3.0 is working :
1 Open Internet Explorer.
Under Internet Options

Security / Local Intranet
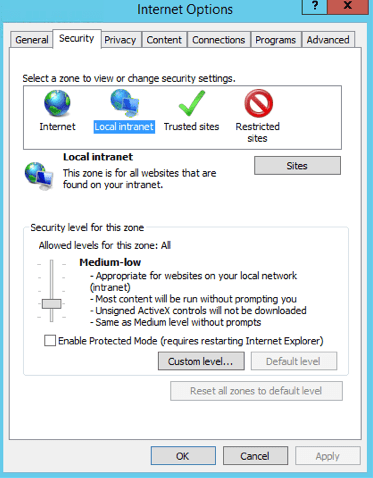
Sites / Advanced
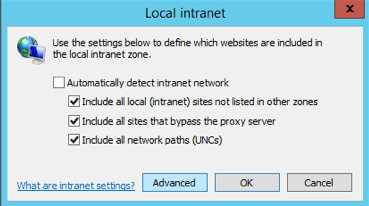
Add *.domain.com to the websites. In our case here we added: *.iwebscrm15.com
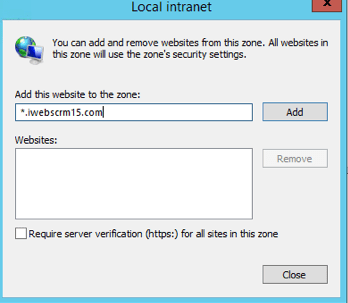
Close all this down when added.
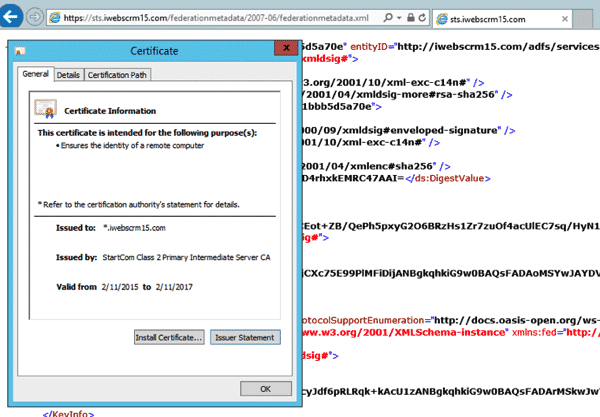
2 Now we need browse to the the federation metadata in Internet explorer to test access is working.
Use this URL below as an example to browse to your own server. Remembering that we set up a DNS entry earlier for “ADFS’ on your domain, thus you should be able to browse to the URL below replacing our domain name with yours and have it access the server we are configuring.
https://adfs.iwebscrm15.com/federationmetadata/2007-06/federationmetadata.xml (Replace your domain name in place of ours)
3. to ensure that no certificate associated with the warning appears, and you can view the certificate to be sure it is showing.

Check the certificate is correct and working by clicking on the padlock looking thing and viewing certificate.
Claims-based authentication configuration CRM 2015 server
After you install and configure the AD FS 3.0 , we need to configure the Claims-based authentication before setting CRM 2015 binding types and the root domain.
1 Open the CRM Deployment Manager.

2 In the Actions pane , click Properties .

3 Click the Web Address page.
4 In the Binding Type , select HTTPS .

5. You can most likely select Apply at this point, and the default internal address for the CRM will work fine. We however we had you created a new A record in the DNS for “internalcrm” and pointed it to this new server. This allows us to user a clear path for the internal URL.
6 For example, internalcrm.iwebscrm15.com:444 for our install. (you can use your own domain internalcrm.domain.com:444)
Note: We use the :444 as this is the HTTPS binding that we applied to the Microsoft Dynamics CRM Website in IIS


7 Click OK.
8 In the Deployment Manager console tree, right-click Microsoft Dynamics CRM, and then click Configure Claims-Based Authentication.
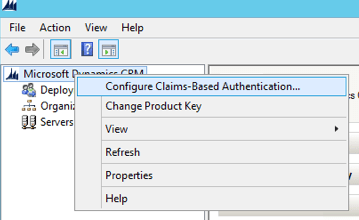
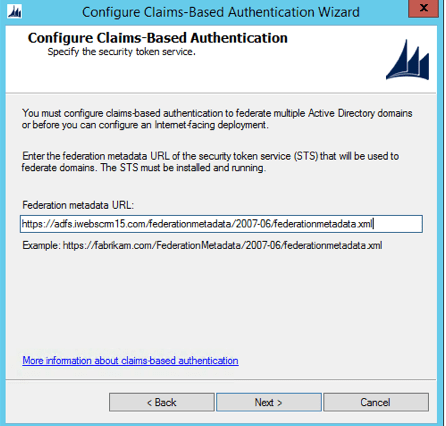
9 Click Next on the Welcome page
10 On the Specify the security token service page, enter the Federation metadata URL, in our case because we setup a DNS record for “adfs” we are going to use that: https://adfs.iwebscrm15.com/federationmetadata/2007-06/federationmetadata.xml
Note: that this is the same URL we tested ADFS was set up correctly on in the steps above. Also note that the step of adding the domain to internal sites in the IE security settings that we did above is an important one! If you can’t hit that URL on the web browser of the server and get a clean XML defined page, then you deployment will not work.
11 Click Next then select the certificate that we created perviously for the *.domain connection

12 Select Next
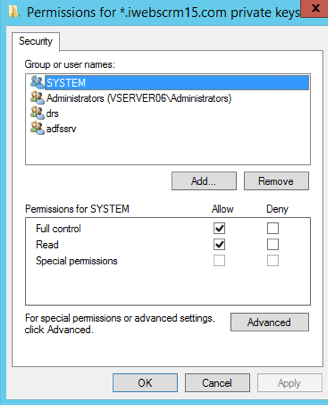
Note: At this point it is possible to get an error something along the lines of “Encrypted Certificate Error”. This is implying that the account used to run CRM does not have access to the Private Key of the certificate being used. Skip forward to point 25 below, and add the service accounts that CRM is using to the private key of the certificate to be used. This will ensure that this next configuration step has access to the certificate. Then come back to this point and continue.

13 Select Apply (BUT – NOT FINISH)

14 IMPORTANT – Click View Log File
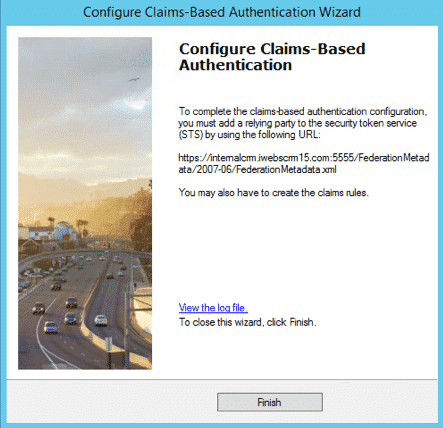
15 Scroll to the end, and Copy the URL from the bottom of the file.

This will be used in the next configuration.
Note: that this is different to the URL used in step 4 above, as it represents the internal URL. Subtle but vital (and the cause of frustration the first 10 times we tried this). In our case the URL looked like this: https://internalcrm.iwebscrm15.com:444/FederationMetadata/2007-06/FederationMetadata.xml
16 Click Finish.
Set the CRM AppPool account and the Microsoft Dynamics CRM Encryption certificate.
17 Right Click the Start Button and select RUN
18 Type MMC and enter

19 Select File / Add/Remove Snap-in

20 Select Certificates and Add

21 Select Computer Account
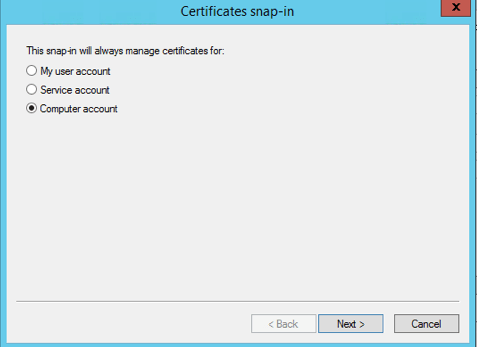
22 Local Computer is selected, so click Finish

23 Expand the console tree / Personal / Click Certificates
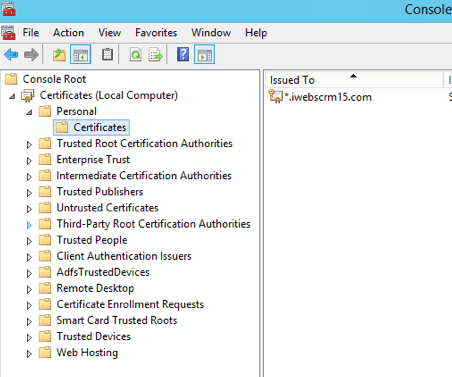
24 Right click the certificate we used for the CRM endpoint, and select All Tasks / Manage Private Keys

25 Select Add
26 Select Advanced

27 Select Find Now
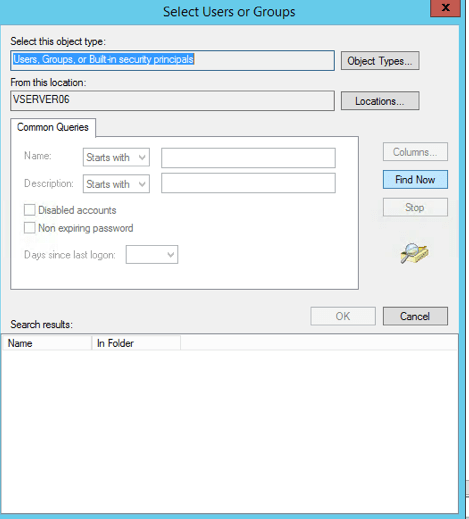
28 Scroll Down and Find the NETWORK SERVICE Account

29 Select OK / OK
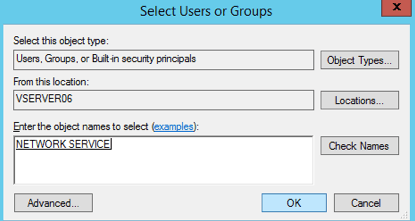
Ensuring that the NETWORK SERVICE has Read Access
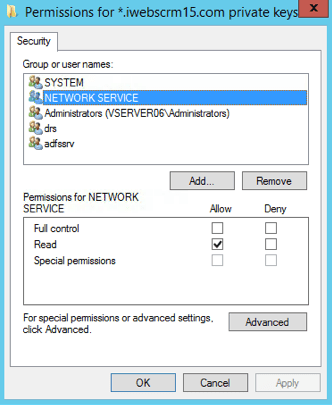
Note: We have used the NETWORK SERVICE account here because that is the one associated with the CRMAppPool used in IIS by default for the Microsoft Dynamics CRM Website that was automatically configured with the CRM setup.
If you are using another account for running the application pool, then you should ensure that this account has access to the encryption certificate. Some details can be found here.
30 Validate that you can browse to the URL above. If you cannot view this in a browser, then have a look again at your permissions on the certificate in relation to the account on the application pool in IIS for CRM. Read above: Claims-based authentication configuration CRM 2015 server.

Once you can browse this URL, you are done if it fails, then repeat the process till you can access the URL on the server in question. Note: Often it is confusion over the port :5555 that defaults in CRM Deployment Manager Web settings and the HTTPS Port :444 that we defined in the binding for the Microsoft CRM Dynamics Website. So double check that you have the correct port set in the Deployment Manager, then run the steps again following that setting.
Claims-based authentication configuration AD FS 3.0 server
After completion of the previous step, the next step we need AD FS 3.0 to add and configure the statement provider trust ( claims Provider trusts ) and the relying party trust ( Relying Party trusts ).
Configure claims provider trusts
Start AD FS 3.0 Management. In the Navigation Pane, expand Trust Relationships, and then click Claims Provider Trusts. Under Claims Provider Trusts, right-click Active Directory, and then click Edit Claims Rules.

In the Rules Editor, click Add Rule, In the Claim rule template list, select the Send LDAP Attributes as Claims template, and then click Next
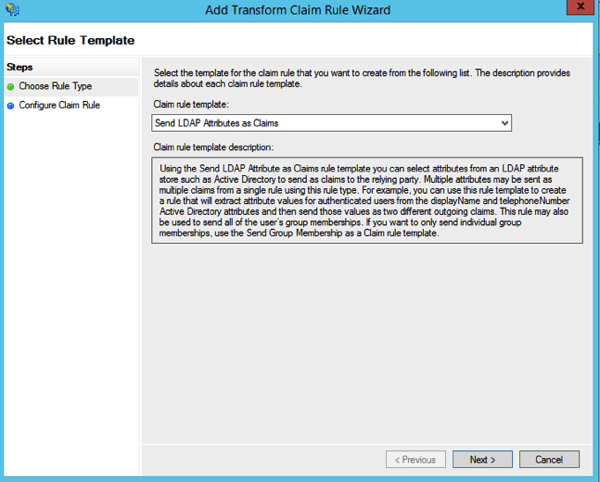
Step10: Create the following rule
Claim rule name: UPN Claim Rule (or something descriptive)
Attribute store: Active Directory
LDAP Attribute: User Principal Name
Outgoing Claim Type: UPN
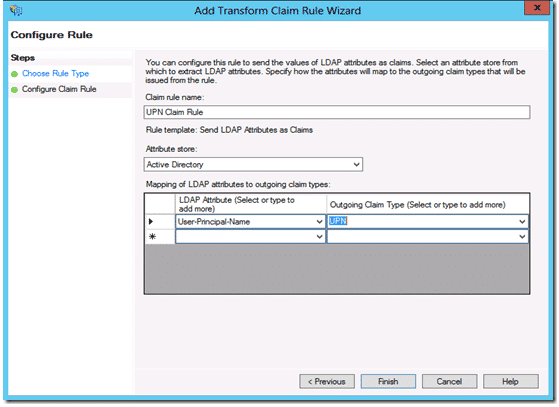
Click Finish, and then click OK to close the Rules Editor
After you enable claims-based authentication, you must configure Dynamics CRM Server 2015 as a relying party to consume claims from AD FS 3.0 for authenticating internal claims access.
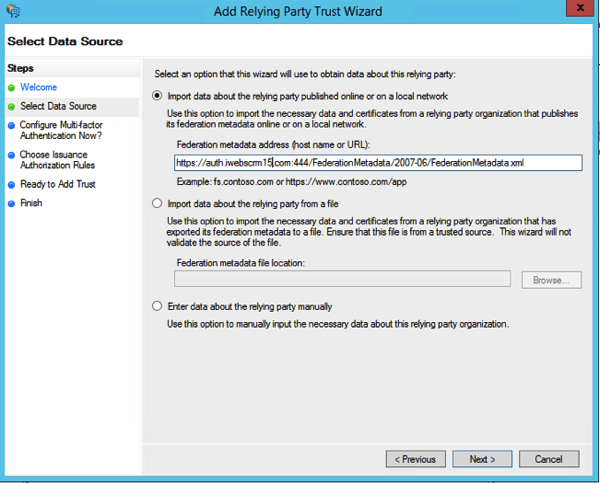
Start AD FS Management. On the Actions menu located in the right column, click Add Relying Party Trust. In the Add Relying Party Trust Wizard, click Start.
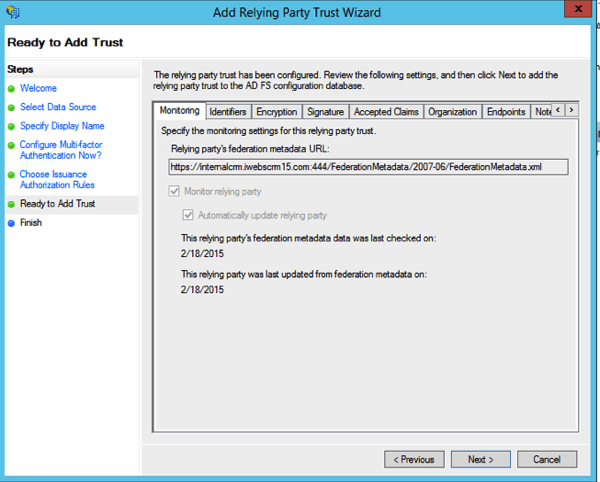
On the Select Data Source page, click Import data about the relying party published online or on a local network, and then type the URL you copied earlier from the log file during the creation of the CRM Claims Based Authentication. e.g. https://internalcrm.iwebscrm15.com:444/FederationMetadata/2007-06/FederationMetadata.xml

On the Specify Display Name page, type a display name, such as CRM Claims Relying Party, and then click Next.

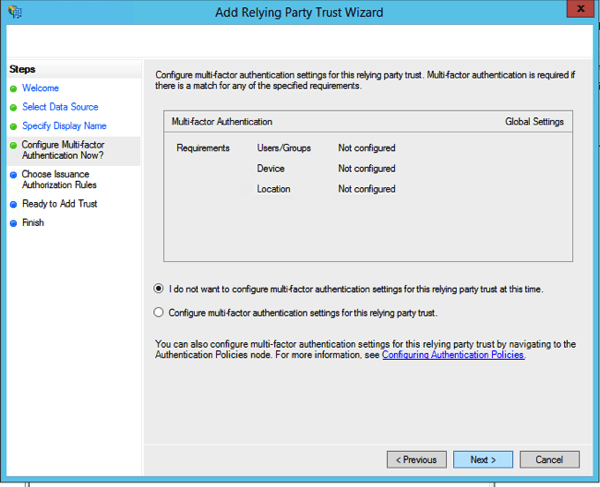
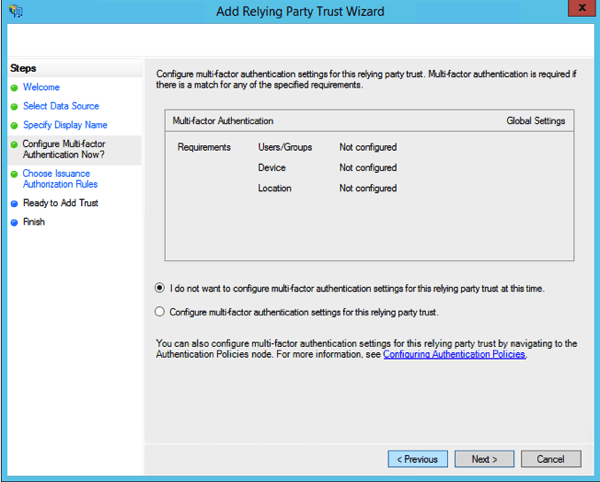
Click Next on the multi-factor authentication options.
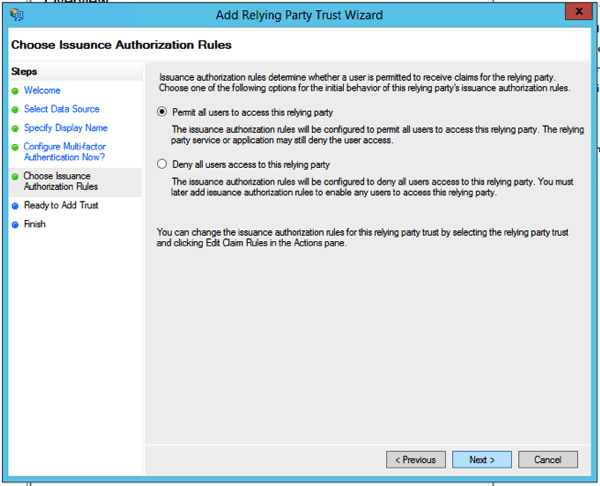
On the Choose Issuance Authorisation Rules page, leave the Permit all users to access this relying party option selected, and then click Next.
On the Ready to Add Trust page Click Next
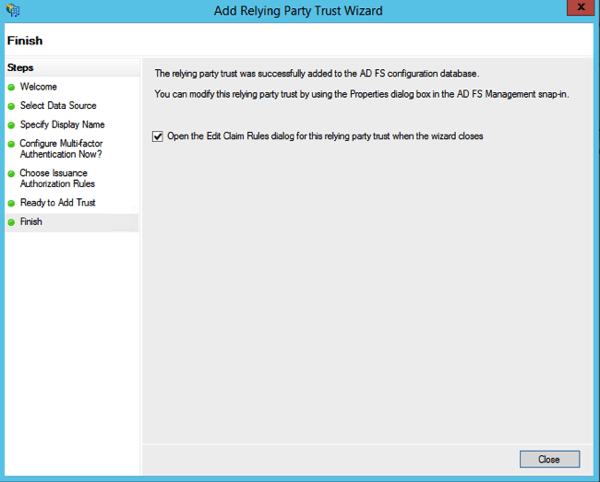
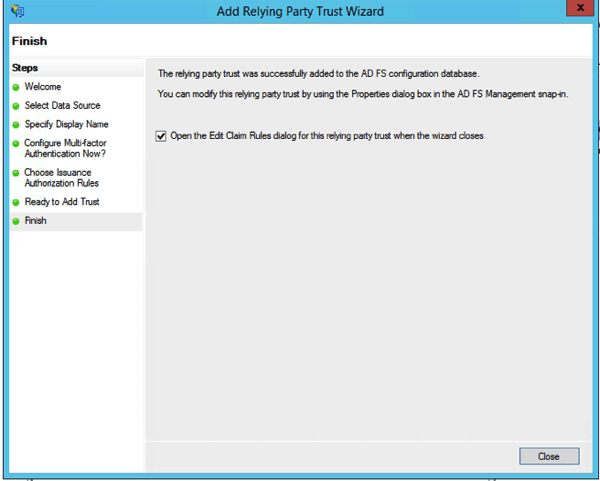
On Finish Page, click the checkbox option to Open the Edit Claim Rules, Next, and then click Close.
The Rules Editor appears, click Add Rule. Otherwise, in the Relying Party Trusts list, right-click the relying party object that you created, click Edit Claims Rules, and then click Add Rule.

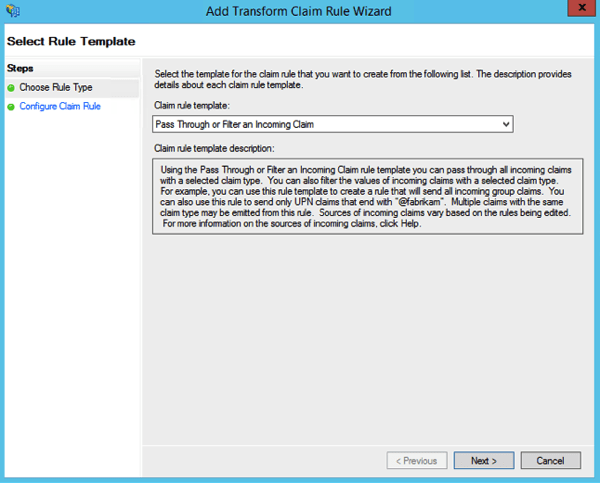
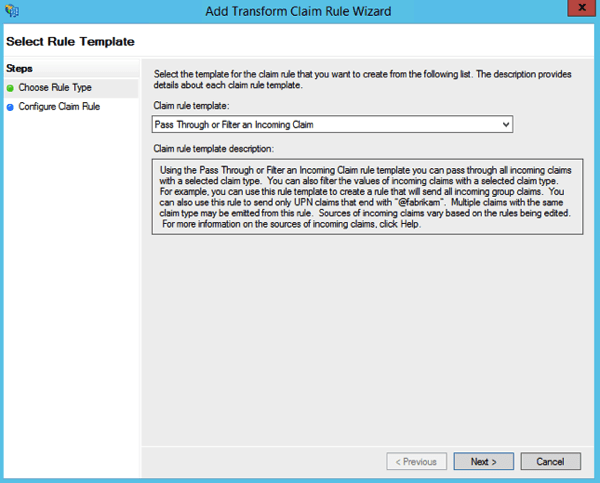
In the Claim rule template list, select the Pass Through or Filter an Incoming Claim template, and then click Next.
Create the following Rule #1
Claim rule name: Pass Through UPN (or something descriptive)
Incoming claim type: UPN
Pass through all claim values
Click Finish.


In the Rules Editor, click Add Rule, in the Claim rule template list, select the Pass Through or Filter an Incoming Claim template, and then click Next
Create the following Rule #2
Claim rule name: Pass Through Primary SID (or something descriptive)
Incoming claim type: Primary SID
Pass through all claim values
Click Finish

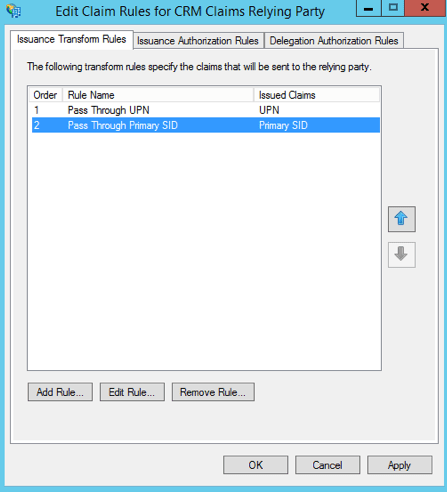
In the Rules Editor, click Add Rule. In the Claim rule template list, select the Transform an Incoming Claim template, and then click Next.
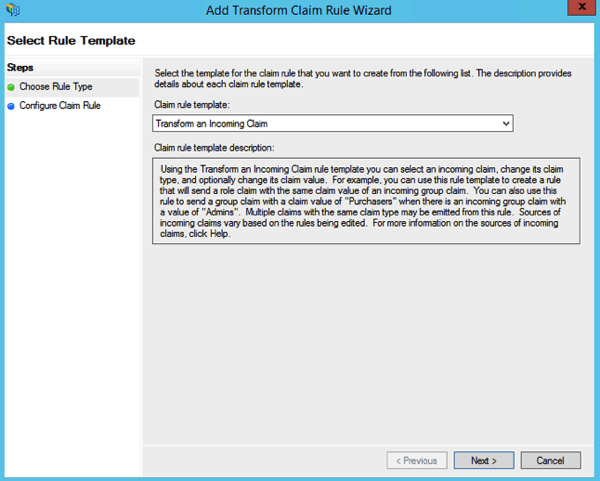
Create the following rule #3
Claim rule name: Transform Windows Account Name to Name (or something descriptive)
Incoming claiming type: Windows account name
Outgoing claim type: * Name
Pass through all claim values

Click Finish, and when you have created all three rules, click OK to close the Rules Editor.

Click OK
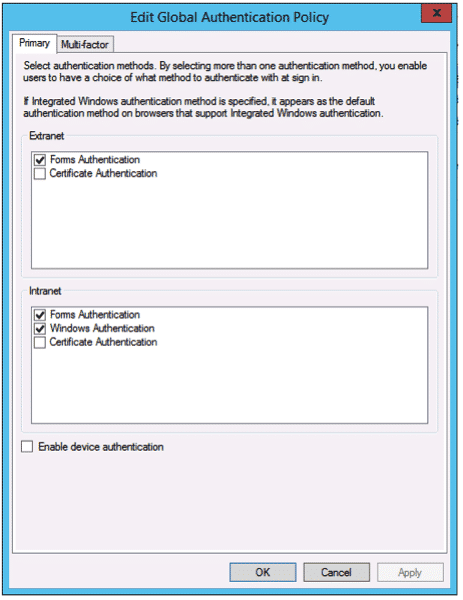
Enable Forms Authentication
AD FS in Windows Server 2012 R2, forms authentication is not enabled by default.
Open the AD FS management console and click Authentication Policies. Under Primary Authentication, Global Settings, Authentication Methods, click Edit.

Under Intranet, enable (check) Forms Authentication.
So now we have claims setup for CRM.
Add the ADFS server to the Local intranet zone.
We previously added the *.domain.com or in our case, *.iwebscrm15.com to the Local intranet zone in Internet explorer on the server. If you have not done this you should do it now. Then:
1. Select the Advanced tab. Scroll down and verify that under Security Enable Integrated Windows Authentication is checked.
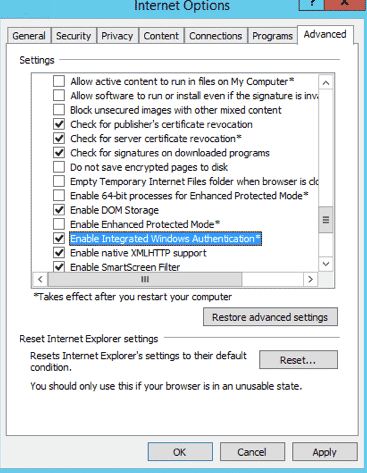
2. Click OK to close the Internet Options dialog box.You will need to update the Local intranet zone on each client computer accessing Microsoft Dynamics CRM data internally.
Specify the security token service
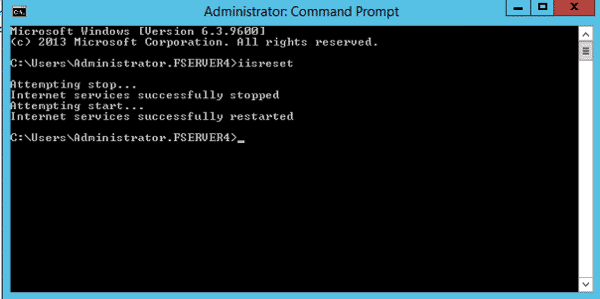
1 Open a command line tool .
2 Enter the following command : ( application, in your own environment, substitute the name of the name of the command line )
c: \> setspn -a http/sts1.iwebscrm15.com fserver4\VSERVER06
fserver4\VSERVER08 = the domain / machine name of the server.
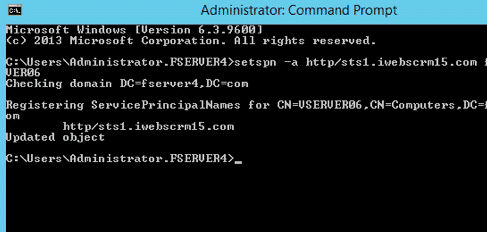
c: \> iisreset
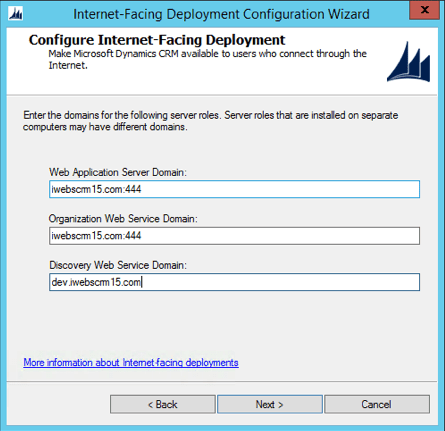
Configure Internet-Facing Deployment in CRM Deployment Manager.
1 Open the CRM Deployment Manager.
2 In the tree structure , right-click Microsoft Dynamics CRM , and then click Configure Internet-Facing Deployment.
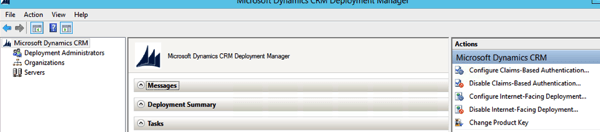
3 Click Next.
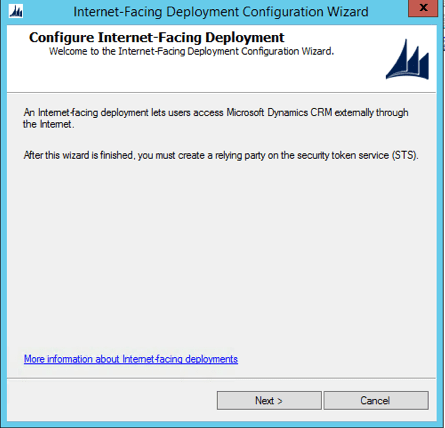
4 Fill in the correct domain information for the Web Application
Thus we use:
- Web Application Server Domain: iwebscrm15.com:444
- Organization Web Service Domain: iwebscrm15.com:444
- Web Service Discovery Domain: dev.iwebscrm15.com:444
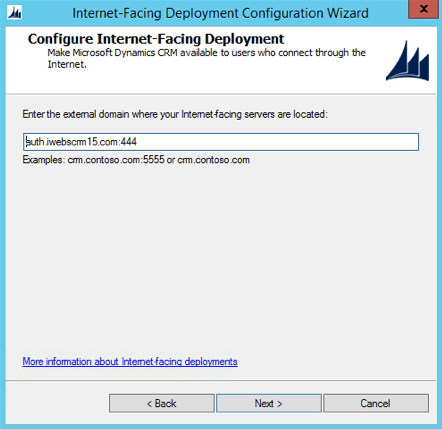
Leave the Default option for the Internet Facing Server Location
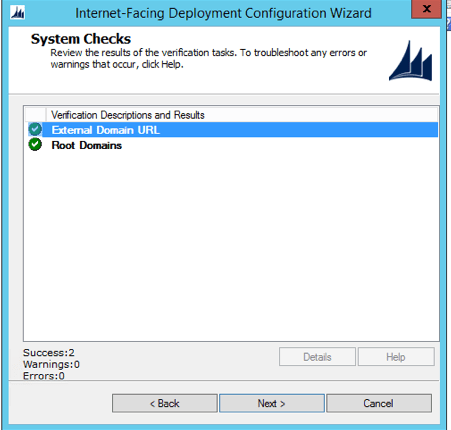
System Checks work
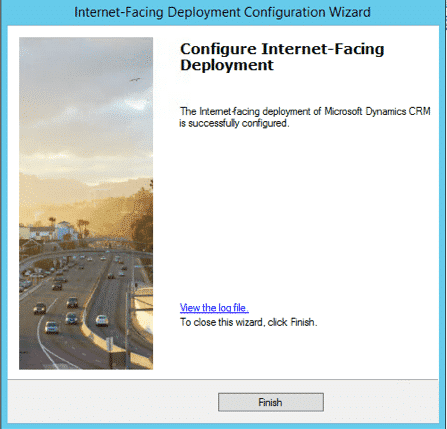
IFD Summary looks like this. Then Apply

Finish
9. Open a command line tool, run: iisreset
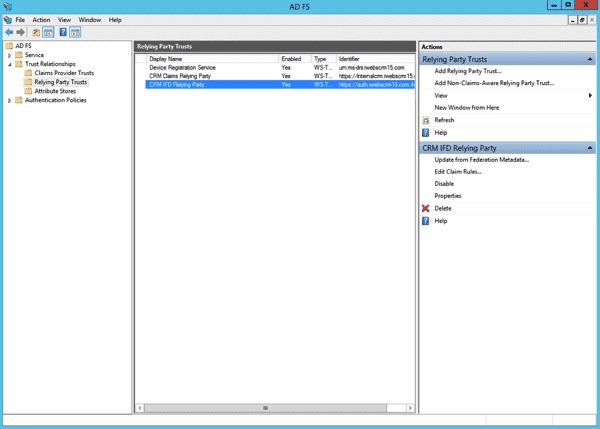
ADFS Relying Party Trust for the IFD Endpoint
Effectively you are creating the third Relying party trust in your deployment and the second that you have manually set up at this point. We are doing this again as this is now for the IFD endpoint.
Step 1: Start AD FS Management. On the Actions menu located in the right column, click Add Relying Party Trust. In the Add Relying Party Trust Wizard, click Start.
Step 2: On the Select Data Source page, click Import data about the relying party published online or on a local network, and then type the URL to locate the federationmetadata.xml file. This federation metadata is created during IFD Setup.
For example, https://auth.iwebscrm.com:444/FederationMetadata/2007-06/FederationMetadata.xml (Remember to replay your domain for ours)
Type this URL in your browser and verify that no certificate-related warnings appear.
Step 3: On the Specify Display Name page, type a display name, such as CRM IFD Relying Party, and then click Next
Step4: On the Choose Issuance Authorization Rules page, leave the Permit all users to access this relying party option selected, and then click Next.
Click Next
Step 5: On the Ready to Add Trust page, click Next, and then click Close.
Step 6: If the Rules Editor appears, click Add Rule. Otherwise, in the Relying Party Trusts list, right-click the relying party object that you created, click Edit Claims Rules, and then click Add Rule
Step 7: In the Claim rule template list, select the Pass Through or Filter an Incoming Claimtemplate, and then click Next.
Step 8: Create the following rule#1
Claim rule name: Pass Through UPN (or something descriptive)
Incoming claim type: UPN
Pass through all claim values
Click Finish
Step 9: In the Rules Editor, click Add Rule, and in the Claim rule template list, select the Pass Through or Filter an Incoming Claim template, and then click Next
Step 10: Create the following rule#2
Claim rule name: Pass Through Primary SID (or something descriptive)
Incoming claim type: Primary SID
Pass through all claim values
Click Finish
Step 11: In the Rules Editor, click Add Rule. In the Claim rule template list, select the Transform an Incoming Claim template, and then click Next.
Step 12: Create the following rule #3
Claim rule name: Transform Windows Account Name to Name (or something descriptive)
Incoming claim type: Windows account name
Outgoing claim type: Name
Pass through all claim values
Click Finish, and when you have created all three rules, click OK to close the Rules Editor.
Now, you should see three Relying Party Trusts in the ADFS Trust Relationships.
Test External Access to CRM 2015 with IFD
Now, you should use the claims certified external access CRM 2015 a. In IE the browser CRM 2015 external address (for example: https://crm2015.iwebscrm15.com:444/main.aspx ), you will see the following pages:

Enter the user name password in the format “domain\username” and pass. You should get in fine.
Additional Tasks for mex Endpoints – Services that connect to XRM
We found after following these instructions, that we could not write services that connected via the endpoint https://your.crm.dom:444/adfs/services/trust/mex. This is due to the CRM Sandbox service using port 808. The solution we applied what one that we wrote for CRM 2013, but is applicable here for CRM 2015: https://www.interactivewebs.com/blog/index.php/crm-2013/adfsservicestrustmex-returns-503-on-crm-2013-windows-2012-ifd-mex-endpoint-fix/
This should be done routinely as it will only pop it’s head up at a later date.
Turn the Firewall Back On
As you may expect, this is a rather important last step
1. Turn on all Firewall Settings as they were at the start
2. Click Advanced Settings

3. Click Inbound Rules / New Rule

4. Select Port / Next

5. Select TCP and Specify Port 444

6. Allow the Connection

7. Domain, Private and Public all ticked.

8. Give it a name like: CRM Port 444
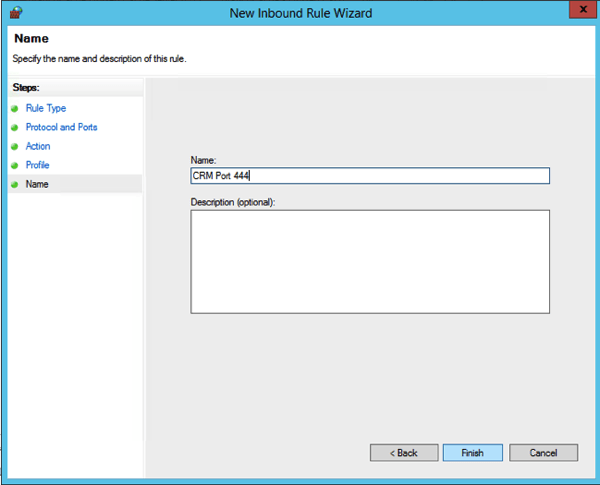
And you are about finished. Remember if in the future you are mucking with something and getting no place. Turn off the Firewall as a starting point. Banging heads with firewalls is a waste of time!
Remember to test access again externally!
Your Feedback and Our Services
Please post a comment or note if you have anything to add about these notes. We welcome feedback that helps us improve them.
If you have a need for CRM 2015 Developer Services, we offer professional services and support for CRM 2015. This includes upgrade services for upgrading from any of the past CRM releases to new ones. We also write custom plugin solutions and are specialists with advanced web services and portals that connect to CRM for many applications. http://www.interactivewebs.com/crm












A lot of great detail in the article, but there are some issues with getting it to work using WinServer 2012 R2 with CRM 2015 and ADFS 3.0…
I have set up ADFS 2.0 successfully for CRM 2011/2013 IFD a number of times so I understand the process. If someone only does what is currently listed in the article, I don’t see how you can actually get CRM to work from the public internet with CRM 2015 and ADFS 3.0.
You wrote “Note: AD FS 2.0 will be installed to the default site, so install AD FS 3.0 , you must have CRM 2015 installation in the new site. (Remember we said that earlier)”.
1. It can’t be 2.0 and 3.0 at the same time It seems this article is a cut/paste job. Have you actually tested by following only the steps listed and had success?
2.From everything I have read ADFS 3.0 does not use or install into IIS Also, the proxy can’t be installed on the same machine as ADFS 3.0.
3. Since it doesn’t install into IIS, you need to install Web Application Proxy (WAP) to front end ADFS 3.0. I don’t see any mention of this in the above article. If you actually got this to work from the public internet with out a WAP server, how did you accomplish it? What am I missing?
Shouldn’t CRM be looking to the public WAP server to get a security token?
Get a security token path flow like this…
User > IIS on CRM Server > WAP > ADFS > WAP > CRM > User
Also, you might consider using port 444 for security and 443 only for CRM. This way you have clean URLs for CRM orgs and don’t need to include the port number and confuse users.
Thanks for the feedback. The initial post was the draft version by mistake. We have updated to the final version of the document. Please check again as this will work if you follow the instructions.
A lot of great post,
I have install CRM 2015 + ADFS 3.0 + IFD Successfully.
I can acces to my CRM with Tablet surface Pro 3.
But I have a problem when i want to add a new user in my CRM 2015 i have this Error :
Unhandled Exception: System.ServiceModel.FaultException`1[[Microsoft.Xrm.Sdk.OrganizationServiceFault, Microsoft.Xrm.Sdk, Version=7.0.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35]]: Server was unable to process request.Detail:
-2147016661
Server was unable to process request.
2015-02-25T17:43:35.9348937Z
ENable trace on the crm server :
>Crm Exception: Message: Server was unable to process request., ErrorCode: -2147016661, InnerException: Microsoft.Crm.CrmException: Server was unable to process request. —> System.DirectoryServices.DirectoryServicesCOMException: A referral was returned from the server. (Exception de HRESULT : 0x8007202B)
— End of the trace of inner exception stack —
[2015-02-26 10:40:18.558] Process: w3wp |Organization:00000000-0000-0000-0000-000000000000 |Thread: 408 |Category: Exception |User: 00000000-0000-0000-0000-000000000000 |Level: Error |ReqId: e4cade07-9f54-4193-ba82-56abf9881c8f | CrmException..ctor ilOffset = 0x7
at CrmException..ctor(String message, Exception innerException, Int32 errorCode, Boolean isFlowControlException) ilOffset = 0x7
at CrmException..ctor(String message, Int32 errorCode) ilOffset = 0x5
at PlatformCommand.CreateCrmExceptionFromServiceFault(FaultException`1 fe) ilOffset = 0x1B
at PlatformCommand.XrmExecuteInternal() ilOffset = 0xF6
at CreateCommand.Execute() ilOffset = 0xC
at EntityProxy.Create(Boolean performDuplicateCheck, Guid auditingTransactionId) ilOffset = 0x0
at EntityProxy.Create(Boolean performDuplicateCheck) ilOffset = 0x7
at SystemUser.Create(Boolean performDuplicateCheck) ilOffset = 0x1F
at EntityProxy.CreateAndRetrieve(String[] columnSet, Boolean performDuplicateCheck) ilOffset = 0x0
at CommandBase.UpdateEntity(Entity entity, Boolean retrieve) ilOffset = 0xAC
at SaveCommand.ExecuteCommand(String commandXml) ilOffset = 0x116
at CommandBase.Execute(String commandXml) ilOffset = 0x13
at InlineEditWebService.Execute(Int32 command, String commandXml) ilOffset = 0xD0
at RuntimeMethodHandle.InvokeMethod(Object target, Object[] arguments, Signature sig, Boolean constructor) ilOffset = 0xFFFFFFFF
at RuntimeMethodInfo.UnsafeInvokeInternal(Object obj, Object[] parameters, Object[] arguments) ilOffset = 0x25
at RuntimeMethodInfo.Invoke(Object obj, BindingFlags invokeAttr, Binder binder, Object[] parameters, CultureInfo culture) ilOffset = 0xCF
at LogicalMethodInfo.Invoke(Object target, Object[] values) ilOffset = 0x4F
at WebServiceHandler.Invoke() ilOffset = 0xC3
at WebServiceHandler.CoreProcessRequest() ilOffset = 0x13E
at SyncSessionlessHandler.ProcessRequest(HttpContext context) ilOffset = 0x39
at HandlerWrapper.ProcessRequest(HttpContext context) ilOffset = 0x7
at CallHandlerExecutionStep.System.Web.HttpApplication.IExecutionStep.Execute() ilOffset = 0x18D
at HttpApplication.ExecuteStep(IExecutionStep step, Boolean& completedSynchronously) ilOffset = 0x15
at ApplicationStepManager.ResumeSteps(Exception error) ilOffset = 0x10A
at HttpApplication.System.Web.IHttpAsyncHandler.BeginProcessRequest(HttpContext context, AsyncCallback cb, Object extraData) ilOffset = 0x5C
at HttpRuntime.ProcessRequestInternal(HttpWorkerRequest wr) ilOffset = 0x16A
at ISAPIRuntime.ProcessRequest(IntPtr ecb, Int32 iWRType) ilOffset = 0x4B
>Crm Exception: Message: Server was unable to process request., ErrorCode: -2147016661
[2015-02-26 10:40:18.574] Process: w3wp |Organization:2a0ead97-17fb-4aae-9862-0be092a6cdc9 |Thread: 408 |Category: Application |User: 00000000-0000-0000-0000-000000000000 |Level: Error |ReqId: e4cade07-9f54-4193-ba82-56abf9881c8f | ErrorInformation.LogError ilOffset = 0x17
>MSCRM Error Report:
——————————————————————————————————–
Error: Server was unable to process request.
Error Number: 0x8007202B
Error Message: Server was unable to process request.
Error Details: Server was unable to process request.
Source File: Not available
Line Number: Not available
Request URL:
Stack Trace Info: [CrmException: Server was unable to process request.]
à Microsoft.Crm.Application.Platform.ServiceCommands.PlatformCommand.XrmExecuteInternal()
à Microsoft.Crm.Application.Platform.ServiceCommands.CreateCommand.Execute()
à Microsoft.Crm.Application.Platform.EntityProxy.Create(Boolean performDuplicateCheck, Guid auditingTransactionId)
à Microsoft.Crm.Application.Platform.EntityProxy.Create(Boolean performDuplicateCheck)
à Microsoft.Crm.Application.Platform.SystemUser.Create(Boolean performDuplicateCheck)
à Microsoft.Crm.Application.Platform.EntityProxy.CreateAndRetrieve(String[] columnSet, Boolean performDuplicateCheck)
à Microsoft.Crm.Core.Application.WebServices.InlineEdit.CommandBase.UpdateEntity(Entity entity, Boolean retrieve)
à Microsoft.Crm.Core.Application.WebServices.InlineEdit.SaveCommand.ExecuteCommand(String commandXml)
à Microsoft.Crm.Core.Application.WebServices.InlineEdit.CommandBase.Execute(String commandXml)
[2015-02-26 10:40:18.574] Process: w3wp |Organization:00000000-0000-0000-0000-000000000000 |Thread: 408 |Category: Application |User: 00000000-0000-0000-0000-000000000000 |Level: Verbose |ReqId: e4cade07-9f54-4193-ba82-56abf9881c8f | MarshalByValueComponent.Dispose ilOffset = 0x7
>AppWebService Destructed: Microsoft.Crm.Core.Application.WebServices.InlineEditWebService
[2015-02-26 10:40:18.636] Process: w3wp |Organization:2a0ead97-17fb-4aae-9862-0be092a6cdc9 |Thread: 415 |Category: Application |User: 00000000-0000-0000-0000-000000000000 |Level: Info |ReqId: 3c9b4baf-54cc-4b6c-bb8a-fd8d5ec88bb9 | Util.TraceMessage ilOffset = 0x79
>UserId ({501C542E-ACA0-E411-80DB-005056AE6BE4}): AppForm.ConfigureControl: QueryString : /Formation/_common/error/dlg_error.aspx?dType=1&hresult=0x8007202B
Any help pls
Regards,
Some people are experiencing this error when adding a single user. Here is a thread discussing a couple of solutions.
https://community.dynamics.com/crm/f/117/t/153348.aspx
Hi,
It’s my Question in Community dynamics CRM 😀
After use trace i found this error :
InnerException: System.DirectoryServices.DirectoryServicesCOMException (0x80072032): An invalid DN syntax was specified.
Regards,
Hi all,
When i check my Server CRM an Server ADFS i found that each server has a LogonServer :
CRM SERVER ===== LOGONSERVER=\\MMV2K5-LDC
َADFS SERVER ===== LOGONSERVER=\\C55V2K5-LDC
How to fix this. Any help pls
Regards,
Hi I have followed your post step by step but I meet an error:
“An error occurred during an attempt tp access the AD FS configuration database:
Error message: MSIS7612: Each identifier for a replying party trust must be unique across all replying party trusts in AD FS configutation”.
How Can I fix this ,Thanks.
I have fixed this issue. You should check carefully about the identifier.You must follow the steps “Configure Internet-Facing Deployment in CRM Deployment Manager” and use the port 444 and use the appcmd command like this:
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:443:adfs.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:443:auth.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:443:dev.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:443:internal.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:443:sts.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:443:talend.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:444:adfs.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:444:auth.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:444:dev.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:444:internal.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:444:sts.style.com’]
appcmd set site /site.name:”Microsoft Dynamics CRM” /+bindings.[protocol=’https’,bindingInformation=’*:444:talend.style.com’]
You may create a wildcard certificate follow this post: http://www.mikeobrien.net/blog/creating-self-signed-wildcard/
Thanks for your post it is very useful. 🙂
Hi,
I followed this post but found this error when login from the web:
“An error occurred
Authentication attempt failed. Select a different sign in option or close the web browser and sign in again. Contact your administrator for more information.
”
can anyone give me some advice?
Thanks.
I have found what caused this problem:
There is a certificate Error:
You can check the Event log.
Hi, has anyone come across a method to have a single url, rather than a internal and external url which will cause issues when users are internal and then external to the company?
My understanding is that with the more recent CRM IFD method, you could not do this. Only suggestion is to hand the entire CRM instance outside the AD login. Thus making it external when working within the network.
Hi. Really good post.
However I have a problem where the internalcrm and the auth relying points both have the same endpoints in the federationmetadata.xml so therefore I have to delete the internalcrm party if I want to access CRM using claims based.
Would appreciate any thoughts.
We have not seen this before, and it is a bit hard to say exactly without seeing what is going on. If you are attempting to follow these instructions exactly, then I would suggest that you wind back and carefully go through the steps again.
Hi Guys
Great Guide I have a slight problem,
internalcrm.domain.com – works a treat
when i try and go to;
crm2015.domain.com
i get an error occurred. contact your administrator for more information
error details: Activity ID: 00000000-0000-0000-1600-0080010000f6
error time:fri 19 jun 2015 16:00:50 GMT
Cookie: enabled
User Agent String: mozilla/5.0 (compatible; MSIE 10.0;Windows NT 6.3; WOW64; Trident/7.0; .NET4.0E; .NET4.0C; .NET CLR 3.5.30729; .NET CLR 2.0.50727; .NET CLR 3.0.30729
im assuming the error message is pretty much nothing, i need to be able to figure out whats causing the issue.
i followed the guide and had no errors during install
any help would be greatly appreciated im literally going mad:)
Sounds like you have not updated the federation meta data: http://www.interactivewebs.com/blog/index.php/server-tips/crm-2015-ifd-adding-a-new-organization-additional-steps/
Thanks for your reply i updated the metadata but no joy. Open a case with Microsoft and after a few hours, the expert is telling me that the site must be exposed via OWA or TMG
im confused as i followed this guide and have not read of any other where it mentions TMG or OWA
Ath My setup is just
Internet > Draytek Router NAT (open ports 444 & 5555) > Server
Am i missing a key component here?
Hi,
Thank you for sharing this step by step instruction. I have done all the steps exactly as described above but I have one issue. Once I supply my credentials over the STS it hangs to https://crm.mydomain.net/login.aspx?ReturnUrl=%2f and then when I remove the /login.aspx?ReturnUrl=%2f part it brings the CRM screen. Can you please tell me what can be the reason for this.
Thanks,
Zack
Sorry Zack, I can’t think what the problem could be. I can only suggest rolling back a few steps and going again. Perhaps someone else reading this has found a solution?
Hi, could you please explain why it is necessary to “setspn -a http/sts1.iwebscrm15.com fserver4\VSERVER06”? At the beginning you set a DNS host “sts” but not “sts1”. Is that a typo? I did not set a SPN at all and basically everything seems to work.
At least there is one thing I am not quite happy with: when I request the CRM using the IFD url, which is in my case “https://test.dev.local” it correctly redirects me to the forms login page of ADFS, but the host/url it redirects me to, is the url of my “internal” ADFS instance.
I would expect that it redirects me to the “external” instance (something like the sts thing as it is also shown here: https://msdn.microsoft.com/en-us/library/gg188590.aspx). I would have to publish the internal instance of ADFS to the internet in the current configuration what I think is not a good idea.
I somehow think this behauvior is related to not setting a SPN 🙂 Here is the configuration of my development environment:
CRM Properties:
Binding Type: HTTPS
Web Application Server: crm.dev.local
Organization Web Service: crm.dev.local
Discovery Web Service: crm.dev.local
Deployment Web Service: crm.dev.local
Claims-Based Authentication Settings:
Federation metadata URL: https://adfs.dev.local/federationmetadata/2007-06/federationmetadata.xml
Internet-Facing Deployment Settings:
Web Application Server Domain: dev.local
Organization Web Service Domain: dev.local
Discovery Web Service Domain: disc.dev.local
External domain: icrm.dev.local
I installed dedicated servers for AD, ADFS, CRM and a Windows 8.1 client machine.
For the servers I set the following DNS hosts:
adfs -> ADFS server
crm -> CRM server
icrm -> CRM server
disc -> CRM server
ssrs -> CRM server (SQL Server Reporting Services)
test -> CRM server (the name of my CRM organization is “Test”)
On ADFS site I set up two Reyling Party Trusts and configured them as you have described it here.
CRM Claims Relying Party: https://crm.dev.local/FederationMetadata/2007-06/FederationMetadata.xml
CRM IFD Relying Party: https://icrm.dev.local/FederationMetadata/2007-06/FederationMetadata.xml
As you might have seen I am not really publishing my CRM to the internet or even a external network. I am somehow simulating the external acces in my internal network. Could this be a problem? Should I setup another network between my CRM server, the Windows 8.1 client machine and the AD machine (with the DNS on it). Should I maybe even setup a second DNS Zone for the external access?
Ok, there is a second thing I am not happy with: when I am using the Windows 8 CRM App I have to login three times and then there comes the ADFS forms login where I also need to enter the credentials. This seems not to be quite normal.
Please give me some hints what’s wrong with my deployment 🙂
Thanks in advance and nice regards!
Yay, at least I found a solution for my second problem: https://technet.microsoft.com/en-us/library/dn531128.aspx#BKMK_AdminToDo
After setting “Turn on dynamic Content URI Rules for Windows store apps” there only pops up the login form of the ADFS, perfect.
Glad you are winning!
Thanks for your comments. The STS.domain.com at the DNS settings stage was a type. In our case we also had an “A” record for a * wildcard, so we never noticed the error in our own environment.
Regards the Windows 8 CRM App – Sorry we can’t help there as we HATE Windows 8 so much, we don’t use it at all so have never used the app.
Why the hell did you remove my comment?!
What the HELL are you talking about? Never removed your post. We had just not approved it yet 😉
Excellent tutorial. You can configure 2 IFD organizations based in your example?
Actually I don’t know.
Hi, Excellent Tutorial I suggest to all my classmates.
I have a question when I log on an error, I have seen the event viewer AD FS and gives me this, I searched a lot but I have not found an answer, have any idea what happens, thanks in advance.
Encountered error during federation passive request.
Additional Data
Protocol Name:
wsfed
Relying Party:
https://orgname.domain.com:444/
Exception details:
Microsoft.IdentityServer.AuthenticationFailedException: MSIS3014: The encryption certificate of the relying party trust ‘https://orgname.domain.com:444/ ‘ identified by thumbprint ’72EBEBD6B7F0ECXXA36CA8AB90B1799FECFF4260’ is not valid. It might indicate that the certificate has been revoked, has expired, or that the certificate chain is not trusted. —> Microsoft.IdentityServer.Service.SecurityTokenService.RevocationValidationException: MSIS3014: The encryption certificate of the relying party trust ‘https://orgname.domain.com:444/’ identified by thumbprint ’72EBEBD6B7F0ECXXA36CA8AB90B1799FECFF4260′ is not valid. It might indicate that the certificate has been revoked, has expired, or that the certificate chain is not trusted.
at Microsoft.IdentityModel.Threading.AsyncResult.End(IAsyncResult result)
at Microsoft.IdentityModel.Threading.TypedAsyncResult`1.End(IAsyncResult result)
at Microsoft.IdentityModel.SecurityTokenService.SecurityTokenService.EndIssue(IAsyncResult result)
at Microsoft.IdentityServer.Web.WSTrust.SecurityTokenServiceManager.Issue(RequestSecurityToken request, IList`1& identityClaimSet)
at Microsoft.IdentityServer.Web.Protocols.PassiveProtocolHandler.SubmitRequest(MSISRequestSecurityToken request, IList`1& identityClaimCollection)
— End of inner exception stack trace —
at Microsoft.IdentityServer.Web.Protocols.PassiveProtocolHandler.SubmitRequest(MSISRequestSecurityToken request, IList`1& identityClaimCollection)
at Microsoft.IdentityServer.Web.Protocols.PassiveProtocolHandler.RequestBearerToken(MSISRequestSecurityToken signInRequest, Uri& replyTo, IList`1& identityClaimCollection)
at Microsoft.IdentityServer.Web.Protocols.WSFederation.WSFederationProtocolHandler.RequestBearerToken(MSISSignInRequestMessage signInRequest, SecurityTokenElement onBehalfOf, SecurityToken primaryAuthToken, SecurityToken deviceSecurityToken, String desiredTokenType, WrappedHttpListenerContext httpContext, Boolean isKmsiRequested, Boolean isApplicationProxyTokenRequired, MSISSession& session)
at Microsoft.IdentityServer.Web.Protocols.WSFederation.WSFederationProtocolHandler.BuildSignInResponseCoreWithSerializedToken(MSISSignInRequestMessage wsFederationPassiveRequest, WrappedHttpListenerContext context, SecurityTokenElement signOnTokenElement, Boolean isKmsiRequested, Boolean isApplicationProxyTokenRequired)
at Microsoft.IdentityServer.Web.Protocols.WSFederation.WSFederationProtocolHandler.BuildSignInResponseCoreWithSecurityToken(WSFederationSignInContext context, SecurityToken securityToken, SecurityToken deviceSecurityToken)
at Microsoft.IdentityServer.Web.Protocols.WSFederation.WSFederationProtocolHandler.BuildSignInResponse(WSFederationSignInContext federationPassiveContext, SecurityToken securityToken, SecurityToken deviceSecurityToken)
at Microsoft.IdentityServer.Web.Protocols.WSFederation.WSFederationProtocolHandler.Process(ProtocolContext context)
at Microsoft.IdentityServer.Web.PassiveProtocolListener.ProcessProtocolRequest(ProtocolContext protocolContext, PassiveProtocolHandler protocolHandler)
at Microsoft.IdentityServer.Web.PassiveProtocolListener.OnGetContext(WrappedHttpListenerContext context)
Microsoft.IdentityServer.Service.SecurityTokenService.RevocationValidationException: MSIS3014: The encryption certificate of the relying party trust ‘https://orgname.domain.com:444/ ‘ identified by thumbprint ’72EBEBD6B7F0ECXXA36CA8AB90B1799FECFF4260’ is not valid. It might indicate that the certificate has been revoked, has expired, or that the certificate chain is not trusted.
at Microsoft.IdentityModel.Threading.AsyncResult.End(IAsyncResult result)
at Microsoft.IdentityModel.Threading.TypedAsyncResult`1.End(IAsyncResult result)
at Microsoft.IdentityModel.SecurityTokenService.SecurityTokenService.EndIssue(IAsyncResult result)
at Microsoft.IdentityServer.Web.WSTrust.SecurityTokenServiceManager.Issue(RequestSecurityToken request, IList`1& identityClaimSet)
at Microsoft.IdentityServer.Web.Protocols.PassiveProtocolHandler.SubmitRequest(MSISRequestSecurityToken request, IList`1& identityClaimCollection)
It appears to say that the certificate is not valid, or is not set correctly with the permissions necessary for the ADFS system to see it. I am assuming that you have renamed the URL, as that looks generic and is unlikely to be the valid cert. – Have you checked that the permissions in the instructions in the certificates area are set on the certificate in question. i.e. you have imported it into the personal certs, and set permissions. If yes, then the account being used by the ADFS server may not be the Network Service account mentioned (from memory) in the instructions.
In fact I changed the URL, of the certificate have not understood very well that permits should check this is another mistake that always leaves you try to login:
An error occurred During an Attempt to build the certificate chain for the relying party trust ‘https://prosupplycrm.prosupply.ec:444/’ IDENTIFIED BY certificate thumbprint ’72EBEBD6B7F0ECXXA36CA8AB90B1799FECFF4260′. Possible causes are That has-been revoked the certificate, the certificate chain Could not be verified as specified by the relying party trust’s encryption certificate or certificate revocation settings is not Within ITS validity period.
You can use Windows PowerShell commands to configure AD FS for the revocation settings for the relying party encryption certificate.
Relying party trust’s encryption certificate revocation settings: CheckChainExcludeRoot
The following errors occurred while building the certificate chain:
The revocation function was unable to check revocation for the certificate.
User Action:
Ensure That the relying party trust’s encryption certificate is valid and revoked Average User.
Ensure That AD FS can access the certificate revocation list if the revocation setting does not specify “none” or a “cache only” setting.
Verify your proxy server setting. For more information About how to verify your proxy server setting, see the AD FS Troubleshooting Guide (http://go.microsoft.com/fwlink/?LinkId=182180).
Good evening,
I found it very good your tutorial, for me it worked following all the steps, but I have two problems:
First, my ISP blockers port 443 and 80 of the internet to resolve this case I to using port 449, however I get an error with the certificate.
Second, my self-signed certificate and, given the cost to adiquirir a wildcard, but even if I add the repository of reliable certificates I got this error, you would have any suggestions for this problem?
And in that field I’m trying to deploy: https://crm2015.edsonsantos.org:449
IIS Needs to be configured with a binding for that port and the HTTPS connection. If you are getting an error, it is likely that this is not bound or not bound correctly.
Using a Self signed cert will always cause errors for people connecting who have not updated their computer to trust the self signed Cert. I did mention that Start SSL is very cheap for a trusted cert. They are something like $49 for verification (I forget exactly) then you can issue as many wildcard certs as you like at no cost.
It could be that your error is associated with the self signed cert and not the binding?
Another alternative is to get a real ISP.
Hello,
I’m hitting an error adding the 2nd relying party trust as I’m hitting “Each identified for a relying party trust must be unique across all relying party trusts in AD FS configuration”
I’m using a different URL for IFD (auth.contoso.com) and internal (internalcrm.contoso.com), but the endpoints in the config point at crmserver1.contoso.com, so the error is generated – I’ve followed the steps above, but there’s no mention of this error, please advise
Hi,
I got around the ” “Each identified for a relying party trust must be unique across all relying party trusts in AD FS configuration” – in the IFD configuration I left out the port 444 on the last URL.
Although I now have 2 issues:
1. I can browse to internalcrm.contoso.local:444, I’m prompted to login and can access Dynamics CRM. How can I get an automatic\single sign-on without the login prompt? Ie already includes *.contoso.local as a trusted site.
2. I can’t login using https://authcrm.contoso.local:444 as I’m redirected to a 404 page not found.
There are no errors in the event logs. I’m using a 3rd party wildcard cert, so not issues there.
Any help is appreciated.
Thanks
The account that you are using the manage the server, needs to be a domain account and not a local administrator account. Have you checked that?
Turned out to be an issue with the accessing URL. My dynamics deployment is called “devcrm” so devcrm.domain.com:444 worked fine (had to create appropriate A record)
authcrm.domain.com:444 still gives the 404
Thanks
the same problem, which was solved by installing ADFS with the default port (443) and installing CRM on a different port (444).
Another problem could be on the relying party trusts, the event viewer of IFD gives you an error? and if so, what is the id of the error?
Good morning,
Do you have steps for how to configure the relying party trust in an account partner organisation so that their users can access Dynamics CRM?
Cheers
Account Partner. – hmmm.. I assume you re referencing them as a business partner. There would be two ways.
1. Setup a domain login for them on your AD. They would need to use your domain/login
2. Set up an AD domain trust between your DNS server and theirs. This could be problematic, but should if configured correctly, allow for login validation via their trusted AD server.
Yes, they’ll be a business partner. I want the partner organisation to authenticate the users, but provide access to my internal crm – isn’t this an ideal use case for ADFS? I’m not quite sure on how to handle the account mappings
Sort of. Perhaps the language you use is a little inaccurate. IFD – allows you to expose your internal CRM system to the internet, and allow others to login via the net to use the system. With IFD, they will still be prompted for a use name and password as you are not allowing them in via a VPN as such. So my thinking is that as long as they have to enter a user name and pass, why not just make it on your domain. Save you a lot of trouble and add no additional trouble to the users.
Thanks for the great tutorial.
We are now applying a second CRM 2015 based Server in our DMZ Network.
The first CRM System is based on Dynamics 2013 and is also configured with ADFS
Problem now is, that the DNS A Records sts, sts1, auth, dev, adfs point to the IP of our first CRM Server in our DNS.
IS there a way to change the default ADFS Sub domains for the second CRM 2015 based Server to have two ADFS based CRM Server in one Domain?
Thanks
Well you could, but it would probably mess with my brain if I was setting it up. That is why when I did it, for our dev environment. We set up. a new domain name for the second server. E.G. https://org.crm2013.com and https://anotherorg.crm2015.com – both of which connect to the same AD server and have seperate OU containers for CRM2103 and CRM2015 respectively. I cannot really see the value on running them on the same domain name as it would just cause you to need to check who is pointing where. You would find yourself constantly pinging IP addresses to remind you what org is where.
Hi
Your tutorial is awesome. I’m having an issue just at the end
1. When I want to set the second Relying Party Trust get “MSIS7612: Each identifier for a relying party trust must be unique across all relaying party trusts in AD FS 2.0 configuration.” I updated it without success.
2. When I try to open the website in my Event Log is this message “A fatal alert was generated and sent to the remote endpoint. This may result in termination of the connection. The TLS protocol defined fatal error code is 10. The Windows SChannel error state is 10.”
Do you have any idea why is happening this?
Thanks
Are you using an SSL cert for connection via RDP to the remote server? Could be related to that if you are. Otherwise I am not sure on this one.
Thanks for the reply. I don’t have any certified for RDP or another service.
I’m going to try configure ADFS again, if the error persist, maybe find another solution.
do you have remote support-consulting with cost?
Thank you
We can provide support services. Best thing to do is to contact us via our website at: http://www.interactivewebs.com – put in a support request chat there, and advise that you are after paid support on CRM 2015 setup.
Hello,
Thanks for this useful guide. I’ve followed this guide and done the following in a single Active Directory domain:
1. Configured claims based authentication for a dev CRM environment consisting of a CRM web server, CRM app server, CRM DB and 2 ADFS servers.
The dev CRM environment works fine – SSO for internal users and forms based authentication for external users.
2. Comfigured claims based authentication for a test CRM environment consisting of 2 CRM web servers, 2 app servers, a DB cluster and I’ve used the 2 ADFS servers above.
The test CRM is proving a challenge – the IFD login works fine for external users, but internal users are redirected to a forms login page, upon entering their credentials they receive a 404 page cannot be found.
Any advice is appreciated.
thanks
That is sounding like an IIS permissions issue. Perhaps you want to confirm that the application pool being used for CRM is on: CRMAppPool – and that this is using: Classic Managed Pipeline Mode – Running under the NetworkService identity, and the the default website is running on the Default Application Pool, and this is using the Integrated Managed Pipeline Mode, with the Identity – ApplicaitonPoolIdentity?
Got around it – as ADFS and CRM are installed on separate servers, CRM is using port 443, if the port is defined in the web address tab in CRM you get those ADFS errors, removing the port works.
Must admit this is a bit fiddly, there seems to be a high number of DNS names which all point to the same address, I’m not quite sure why they’re all needed,
Thanks
Hello,
I’ve configured this and it works :-), thanks for the guide.
I’ve now added a second CRM organisation (test2), the internal URL works fine: https:///test2
The external URL https:///test gives a 404 page not found.
My original URLs still work as normal:
https:// – SSO
https:// – forms based authentication
What do I need to do to ensure that my second CRM environment is available via the external URL?
Thanks in advance
I’m thinking that you have not got the correct settings in IIS for the redirection.
Hi,
We have a DMZ domain, plus an internal and external ADFS environment. Is it possible to do the following:
1. Have users authenticated against our DMZ domain
2. Have the users passed through to our internal CRM environment via the ADFS DMZ domain?
Thanks
Has anyone run into trying to authorize the Scribe Insight ETL tool with its Dynamics CRM API adapter to connect to CRM Online (Azure/Cloud CRM)? We run ADFS federated for our tenant of Office365 and now CRM, and the users can authenticate just fine, but we can’t seem to get Scribe to connect to the Microsoft API’s in the cloud with a federated account… it works fine with an account that is just local to our tenant, but then if we want to use a Synced group as the security group governing access to the CRM instance in the cloud, that account breaks since we can’t put it in the group (AADS/FIM removes it since it isn’t present in the on-premise group, where we want/need to maintain the list of valid CRM users in each instance using our existing AD tools). Thanks for sharing a response if you’ve run across this unusual use-case.
Thanks for step by step document, just awesome
Most Welcome.
Hi could you help me, I already done config the ADFS for CRM Internal Access using Claim Based. but comes error in certificate.
Trace CRM:
Error Details: ID4175: The issuer of the security token was not recognized by the IssuerNameRegistry. To accept security tokens from this issuer, configure the IssuerNameRegistry to return a valid name for this issuer.&RequestUri=/default.aspx&user_lcid=1033] from [10.99.20.60] entered Authentication Pipeline.
Then I follow reference
To disable the Extended Protection for Authentication feature in AD FS 2.0
Set-ADFSProperties –ExtendedProtectionTokenCheck None
and then do this:
net stop adfssrv
net start adfssrv
But don’t understand why the ADFS service doesn’t want to start again. Please help…
There is data on this here: https://support.microsoft.com/en-us/kb/2686840
Hello,
CRM2016+IFD : done but I have a question about login authentication ADFS format : can we type only username without domain name or with UPN format ?
Thanks in advance.
Hervé.
You can, but you muse set this in the ADFS to allow it. Possible and a lot of data on the net to enable this.
Ok thks for response, and yes I use ADFS, of course, but how can I modifiy login auth to user only username ?? by modifying the rules ?
THKS
Herve
Thanks for the excellent post. I was able to setup an IFD of CRM2015 on Windows Server 2012 R2.
You’re most welcome.
Quick question – does the port 5555 matter? The reason I ask is that I have an install that I’ve been playing with on port 80 and didn’t want to do a whole new install to trial ifd
Depends on what else you are doing on port 80. The answer is no, but you may need to be careful if you also plan to have port 80 used for other normal web services.
other web services such as? currently I had planned for just a dedicated server for the CRM…